
Zero Trust Begins with Identity
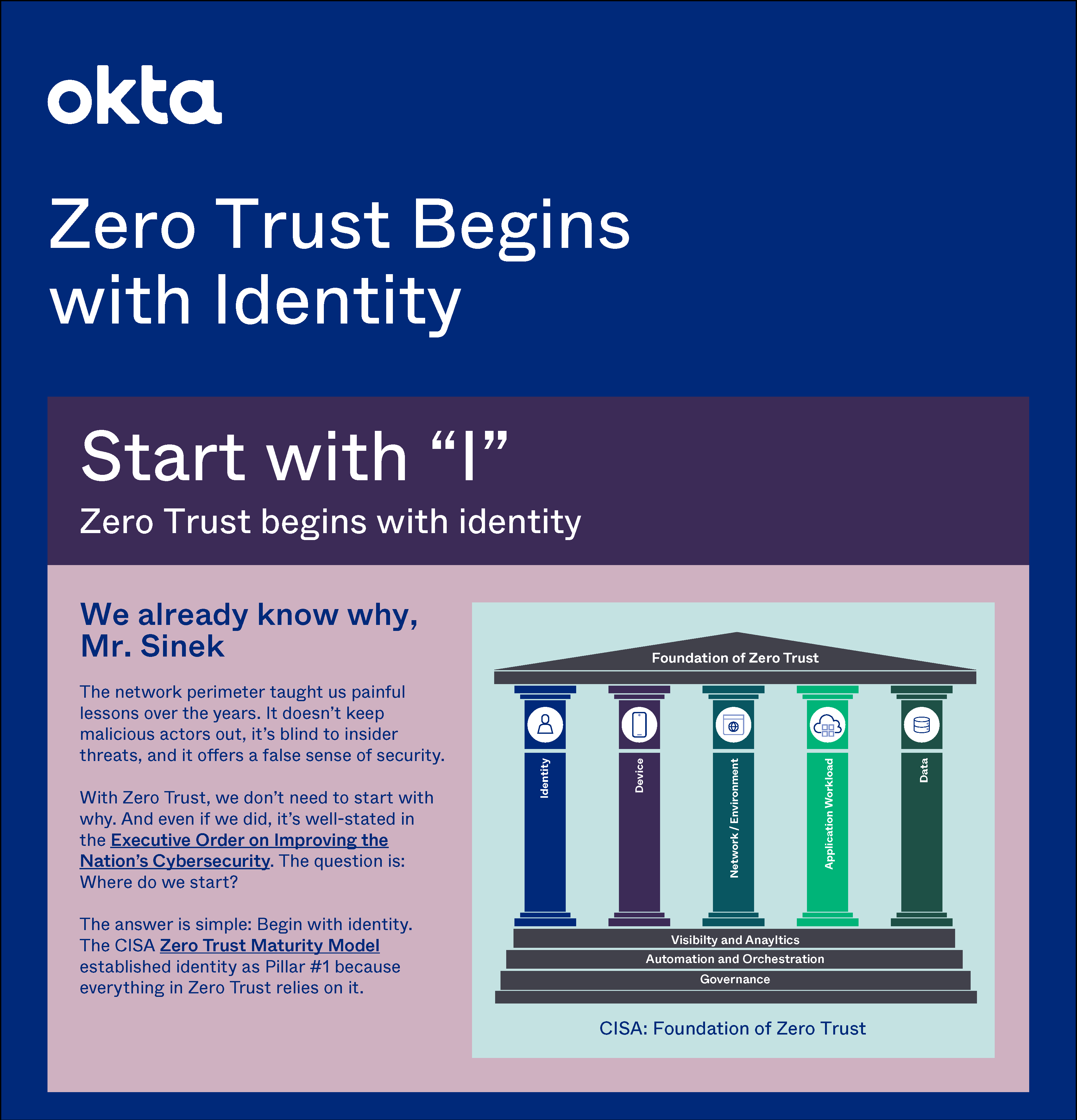
IThe Cybersecurity Executive Order requires every federal agency to adopt zero trust, and the CISA Zero Trust Maturity Model aids the transition. It shows five pillars of zero trust, and the first is Identity. Learn why zero trust begins with identity, and how to quickly achieve optimal identity maturity.
Download Infographic