Author: wpAdmin
-

Modernizing Higher Education Data Management with IIJA Funding
| | | RESOURCE | | | ISSUE BRIEF Modernizing Higher Education Data Management with IIJA Funding Higher education institutions have diverse and often siloed data stored in legacy infrastructure. And while campuses made rapid updates to their data management infrastructure during the pandemic, many are now assessing needs and starting more strategic, long-term planning. A…
-
Create 3D assets with a 2D skillset using the Adobe Substance 3D Collection_UE
Create 3D assets with a 2D skillset using the Adobe Substance 3D Collection_UE The 3D revolution is here — and just in time for today’s graphic designers, who are under pressure to create customized, realistic assets to support a wide range of business needs and audiences. To learn more about the next generation of 3D…
-
3D Starter — Explore the Foundations of 3D Design
3D Starter — Explore the Foundations of 3D Design 3D is fast becoming the go-to choice for creating product mockups, brand visualizations, packaging designs, and more — and the pressure has never been higher on designers to integrate 3D design into their workflow. Fortunately, the tools to do so have never been more powerful or…
-
Moving business outcomes forward — making the case for 3D design tools_UE
Moving business outcomes forward — making the case for 3D design tools_UE Learn how to sell stakeholders on the business value of 3D design tools by speaking their language and addressing what they care about most. In this workbook, you’ll: Identify your most important business goals Align 3D design investment to those goals Learn how…
-
3 Real-World Challenges Facing Cybersecurity Organizations:How an Exposure Management Platform Can Help
3 Real-World Challenges Facing Cybersecurity Organizations: How an Exposure Management Platform Can Help Implementing an exposure management program enables security professionals to better allocate time and resources so they can focus on taking the actions that legitimately reduce their risk. Read this whitepaper to learn about: 3 real-world challenges facing cybersecurity organizations The building blocks…
-
Access new levels of creative freedom and control with 3D-powered design
Access new levels of creative freedom and control with 3D-powered design Product design. Packaging design. Virtual photography. These are just a few fields undergoing radical transformation thanks to 3D design tools that are easy to use and impossible to outgrow. Learn how today’s creatives are putting them to work to scale high-quality, photorealistic asset creation…
-
How to Generate Predictable Pipeline from ABM
How to Generate Predictable Pipeline from ABM Disparate, siloed systems that don’t talk to one another and have no way of connecting vital information can cripple B2B marketing teams. Learn how to use a Demand Acceleration Platform to connect your core martech systems and channels. This guide covers how to connect siloed data and systems…
-
The Demand & ABM Technology Convergence
The Demand & ABM Technology Convergence Discrete account-based marketing (ABM) and demand generation marketing approaches and technologies have co-existed in B2B marketing organizations for the past several years. But marketers need to get ready for what’s coming. ABM and demand marketing are converging, and the impact is going to be significant-especially for marketing operations teams.…
-
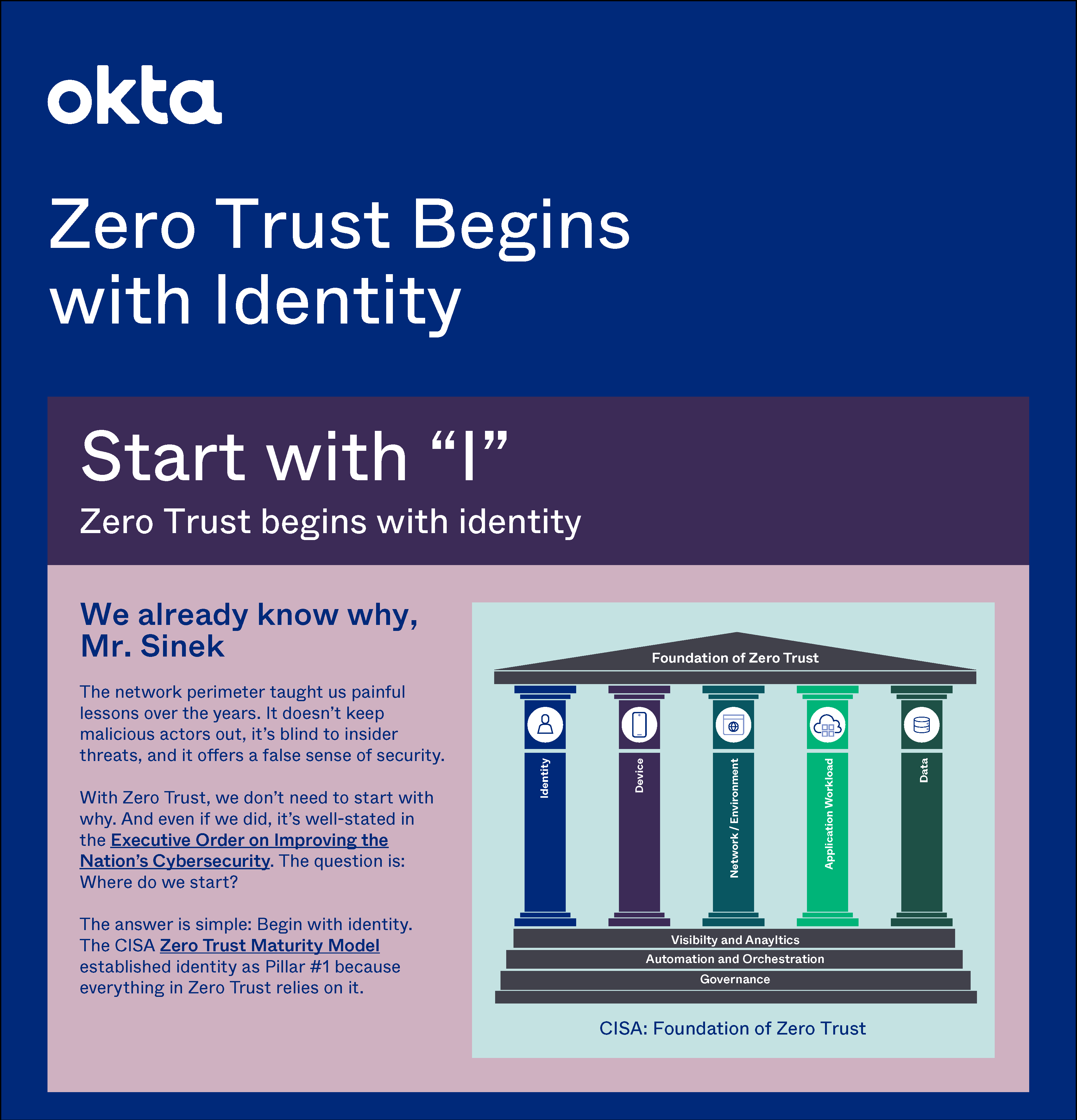
Zero Trust Begins with Identity
Zero Trust Begins with Identity IThe Cybersecurity Executive Order requires every federal agency to adopt zero trust, and the CISA Zero Trust Maturity Model aids the transition. It shows five pillars of zero trust, and the first is Identity. Learn why zero trust begins with identity, and how to quickly achieve optimal identity maturity. Download…
-
Zero Trust Solutions: What Agencies Can Do Today to Meet Tomorrow’s Challenges
Zero Trust Solutions: What Agencies Can Do Today to Meet Tomorrow’s Challenges In the wake of rising geopolitical tensions, the threat of cyberattacks on agencies is becoming inevitable, forcing the federal landscape to rethink how it secures applications and data. To support this mission and create a more resilient cyber infrastructure, President Joe Biden signed…